|
|
ACS equipment
Equipment ACS is a complex and multi-faceted collection of instruments, devices, and software used to manage and control access to a dedicated premises and areas, relocation of staff and visitors, the duration of their stay in the facility, etc.
Reader ACS, ACS cards, ACS module and other equipment of access control systems
The ACS equipment are used in monitoring systems and access control systems (ACS), depending on the specific objectives of a company's management and security service’s object. Anyway, any access control system consists of the following essential elements:
- funds of identifications (ACS cards, chips, etc.)
- Master Controller
- reader on the "input" and \ or "output"
- reset button (usually the "Output")
- unlocking or locking device (the turnstile, barrier, etc.)
- Sensors of security systems (volumetric sensors, motion detectors, etc.)
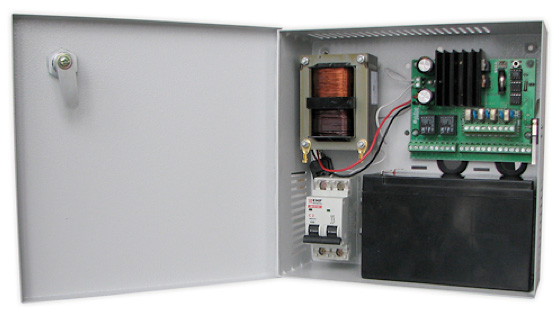
- Uninterruptible power supply (UPS) with emergency power system
- software programming
The Reader ACS is an electrical or electromechanical device (appliance), adapted to read codes with identifiers and their transmissions to the ACS controller for further processing.
They are divided into contacts and non-contacts: contacts are used when it’s necessary for the reading a physical contact with the identifier (magnetic readers readers Touch memory), and the non-contact reading of data occurs at a distance (barcode readers, proximity readers).
A Separated blocks allocated by biometric readers (retina of the human eyes, fingerprints, and other unique physiological parameters of human), characterized by high reliability: they can not be stolen or given to the wrong person, as an access card or keys.
Proximity-reader PLR2
 Proximity-reader PLR2 is designed for non-contact reading of a unique code of Proximity-card, and transfer it to the controller. PLR2 uses a comprising of Legos systems to identify the user by the code of its Proximity-card. Proximity-reader PLR2 is designed for non-contact reading of a unique code of Proximity-card, and transfer it to the controller. PLR2 uses a comprising of Legos systems to identify the user by the code of its Proximity-card.
Consignment of the non-contact reader PLR2
The device is a separate remote unit with a connection cable. Touch Memory Interface or Wiegand-26. Made in a plastic case. In the case it’s posted a board with LED and audible indicators. The reader operates at a frequency of 125 kHz. PLR2 powered by the controller to which it is connected. Read Range - 10 cm.
Non-Contact Proximity PLR3 with a indicating band
 Currently there are the following models: Currently there are the following models:
- PLR2EN - Proximity card reader standard, EM-Marine, and HID (Touch Memory/Wiegand-26 Interface).
- PLR2M - MiFire card reader .
Reader-pocket CH2E
 Reader-pocket in presence of EM-Marine card is designed for remote control. The reader is used to monitor the presence of user location indoors and the inclusion of automatic controller at lowering the access card into the reader and further its presence in the reader. Reader-pocket in presence of EM-Marine card is designed for remote control. The reader is used to monitor the presence of user location indoors and the inclusion of automatic controller at lowering the access card into the reader and further its presence in the reader.
ACS cards and their main types
Access control cards are the most common identifiers. In it turn, the most promising of them today are considered to be non-contact RFID Proximity card: they operate at a distance, uncritical to the clear positioning of the object, and therefore stable and effective. The principle of their operation is based on the activation and transfer of electromagnetic energy directed from the reader, resulting in what ACS "decides" to skip or not the cardholder in a particular area of the access.
Another popular type of cards is the key-fob «Touch memory» - a device resembling a tablet in which is mounted an electronic chip. To activate the key, it’s necessary to attach the tablet to the reader.
Furthermore, the widespread magnetic card, the information contained in them is in the magnetic layer. Magnetic cards less wear out, however, their significant negative - in a limited period of validity: a such card mustn't be reprogrammed.
ACS Controllers
Management Controller L5-series
Controllers in this series are designed to build high-security system buildings. Each controller allows to manage a single point of passage or control a set of security and fire alarms. L5 Series controllers are used in offices and commercial buildings, entertainment centers, hospitals, stadiums, industrial and other enterprises.
At the moment, there are the following ACS controller models :
- L5D32 (L5D04) — elevator controller if access "Door" «Дверь-Dver» (models with memory for 32,000 and 4,000 people / events);
- L5TC32 (L5TC04) — elevator controller of access "Turnstile" «Турникет -turniket» (models with Card Slot and memory for 32,000 and 4,000 people / events);
- L5T32 (L5Т04) — — elevator controller of access "Turnstile" «Турникет -turniket» ;
- L5G32 (L5G04) — elevator controller of access "Gates. Barrier " «Ворота. Шлагбаум – vorota. shlabagum» (models with memory for 32,000 and 4,000 people / events);
- L5L32 (L5L04) — elevator controller for lift (models with memory for 32,000 and 4,000 people / events);
Controllers OPS:
- L5764 — firefighter- security Controller (64 firefighter- security addresses and memory for 32,000 people / events);
- L5632 — firefighter- security Controller (32 firefighter- security addresses and memory for 4,000 people / events);
Controllers for high-security areas:
- L5D32P — elevator controller of access "Door" «Дверь-Dver» with double identity of the user (proximity card + pincode);
- L5D32P2 — elevator controller of access "Door" «Дверь-Dver» with double identity of the user (according to the rule of 2 persons);
- L5S32P — elevator controller of the gateway cabin with double identity of the user (proximity card + pincode);
- L5S32F — — elevator controller of the gateway with triple user identification (proximity card + pincode + fingerprint).
The button "Exit"
Buttons RTE (Request To Exit) or simply - "Exit" are used for manual opening of the actuator to provide the exit from the premises without using cards. In this case, the controller registers in the memory only the fact of intersection point of the passage.
Unlocking or locking devices (electromagnets “solenoids”, turnstiles, barriers, etc.)

Lock ML-194
CLE Converter
 The Converter is designed to convert signals of of the protocol TCP/IP in a bi-specific signals of Interface link controllers Legos (LBus). The converter is connected to a local area network. Exhibited by the control of the computer IP-address, which is used when referring to the system of this converter. The Converter is designed to convert signals of of the protocol TCP/IP in a bi-specific signals of Interface link controllers Legos (LBus). The converter is connected to a local area network. Exhibited by the control of the computer IP-address, which is used when referring to the system of this converter.
Status Sensors of the security facilities (Reed, laser motion sensors, volumetric sensors, etc.)
 The sensor detects the opening of doors, the controller processes the event and passes it on to the software. The sensor detects the opening of doors, the controller processes the event and passes it on to the software.
ACS module and its role in the organization of access control
ACS module - it is nothing like the software and the other utilities. Thus, the basic elements of security and control modules Legos are acs modules, designed to solve the following tasks:
- System Setup
- monitoring of facilities, efficient delivery, processing and storage of data
- System management
- adoption of standardized automation solutions
- Integration with other automated systems
Each module implements a particular part of the overall functionality of the system. At a minimum set of software modules includes a basic set of software, system setup (configuration tool), as well as license to operate a single point of entry. A set of modules can be arbitrary and vary depending on the specific needs of the customer. The modules allow devices to conduct asynchronous recording of parameters, which is produced by one in each controller, so the system does not fail, and can automatically adjust their settings. In any case, the software ACS largely accelerates and simplifies the procedure for issuing and deleting the passes, allows to improve the monitoring program of the object, making it reliably protected.
The company " Flylink" works with the best suppliers of equipment for access control systems, and is a certified installer of many of them. That's why, referring to our experts for the selection and installation of ACS, you will ensure the material’s safety, intellectual and other values, by ordering any movement of personnel and equipment within your facility.
|
PHOTOALBUM OF OUR PROJECTS
Cabling Systems.
Fiber Optic Lines.

Wireless Networks.

Powering and Lightning.

Security Systems.

NOTE
Design and installation of SCS. SCS - professional building structured cabling systems. Corporate computer networks - the organization, laying, setting up, upgrading or repair.
Complex security systems - CCTV installation (video surveillance) and access control systems will improve the efficiency of a warehouse, cottage, office shop and other sectors of business.
WMS warehouse management system. Integrated WMS implementation of various infrastructures - access control, electric power, data centers, security systems, video surveillance, high-precision equipment ...
|